Background
Update: The API has been extended to apply to Evaluations as well as Entities.
Update: The API has been extended to apply to Teams. See Teams
Update: We allow updating of Access Requirements by the ACT. We allow Access Requirements to apply to Folders as well as Files. Entities inherit any access restrictions applies to Folders which contain them.
Update: We add inheritance of access requirements: Each entity inherits the access requirements of its ancestors (e.g. the Folder(s) containing a given File).
IRB-approved versions of all of the 'data access documents' :
Summary:
- Data layer access in Synapse requires one or more approval steps.
- In Synapse granting data access is synonymous with providing the URL to the stored data.
(This URL may have an embedded access token.)
- Currently (i.e. as of Jan. 2012), the backend Prior to this work, the back end has a representation of EULAs and of Agreements (i.e. that a particular user agrees to a EULA)
- The work flow logic for creating the agreement is embedded in the Web client, so other clients would have to maintain duplicate logic. Specifically, the web client has the following logic:
1) When a user tries to download a layer, the Web client checks whether the parent dataset has an associate EULA;
2) If there is an EULA, the web client checks whether there is an Agreement, owned by the User and referencing the dataset and EULA;
3) If there is a EULA but no Agreement, the web client prompts the User to sign the EULA, creates the Agreement, then allows the download.
...
Tier 3: (Tier 1) + (Tier 2) + User access must be requested/approved through an Access and Compliance Team (ACT).
Design
...
Database
- We add a 'Download' permission, as distinct from 'Read' permission to entity access control lists.
- In order for a user to get the location field(s) of an entity, they must have Download permission.
Workflow Model
Design Assumptions
Things the client should NOT 'know'
- what requirements need to be met to obtain a permission (e.g. you need to sign a EULA to access a Layer's location)
- what requirements have/have not been met by a User (e.g. whether a EULA has been signed)
- whether it can access a certain field of a certain entity
Things the client SHOULD 'know'
- how to fulfill a requirement (e.g. if a EULA needs to be signed, knows how to retrieve and display the EULA, get it signed, and submit the appropriate request to the repo service)
Design Approach
Field access service
- Given an entity, find out what access on what fields the user has
The permission service
- Add a new 'permission' service which (1) grants permissions if requirements are met or (2) otherwise reports what requirements need to be met. E.g. POST /layer/101/permission/Download, where '101' is an entity ID, would either (1) grant the requested permission (Download) if the user meets the requirements or (2) return a (401) response with a body of the form
| Code Block |
|---|
{
[ {type:EULA, params:{uri:/eula/987}, msg:status-msg}, {type:EULA, params:{uri:/eula/654}, msg:status-msg}, {type:ACT, params:{uri:/act/321}, msg:status-msg}]
}
|
listing the unmet requirements.
(Optionally, just one of multiple unmet requirements could be returned, allowing the server to control the order in which requirements are considered by the client.)
There are three parts to a requirement:
- type: from an ENUM, e.g. 'EULA', 'ACT'.
- params: a map of parameters used by the given 'type'. The client needs to know what to do for each enum, and how to use its parameters. This will be documented in the developers' API.
- msg: An optional status message, suitable for display to the user.
If a requirement has no type or params but has a message, then there is nothing for the user to do and the message helps explain why, e.g. {msg:"ACT approval pending"}
Permission Manager
The repository service will have a Permission Manager, which computes the response to the permission request from a given user for a given entity. E.g. if a Layer required EULA 987 to be signed for a user to access it, and EULA 987 is not yet signed by the user, then the Permission Manager adds this requirement to the response to thepermissions request. The unmet requirements are stored *implicitly* in the state of the repository services, and the PM determines the unment requirements upon request.
Object Model for Permission Requirements
An entity may have Requirement child entities (or should these be properties of an entity?). These entities (properties?) contain the details of what is required to obtain specific permissions on the object (e.g. <Download,EULA,/eula/987>). The PM refers to these entities (properties?) to make its assessment.
Additional Services
- requirements CRUD services: allows the owner of an object to craft requirements for an object (or should this be rolled into the current permissions management?)
Tier 1 Approval Process
Here the user signs the Tier 1 agreement upon account creation. (Omitted are the steps in which the client retrieves the schema and the current ACL to determine that the user doesn't have the necessary permissions.)
Tier 2 Approval Process
This approval requires two hurdles, the Tier 1 agreement plus a new agreement which may be specific to the requested layer.
How do you revoke approval?
1) remove the <User, Permission> from the layer's ACL.
2) delete the permission requirement from the entity.
Tier 3 Approval Process
Here we have the added complexity of an external ACT.
We have tables for Requirements and Approvals: ACCESS_REQUIREMENT contains the requirement information, while NODE_ACCESS_REQUIREMENT 'joins' it to the JDONODE table, saying what entities are affected by the requirement. ACCESS_APPROVAL has foreign keys to ACCESS_REQUIREMENT and principal. The first imposes a requirement for access to the node. The second fulfills the requirement, for a given principal. The requirement and approval tables have an "ENTITY_TYPE" field (populated from an ENUM) and a "SERIALIZED_ENTITY" field, a BLOB, allowing them to have variable content, so they can be used for Tier 2 or Tier 3 requirements.
Below we omit the primary key and foreign key constraints for simplicity.
| Code Block |
|---|
CREATE TABLE `ACCESS_REQUIREMENT` (
`ID` bigint(20) NOT NULL AUTO_INCREMENT,
`ETAG` bigint(20) NOT NULL,
`CREATED_BY` bigint(20) NOT NULL,
`CREATED_ON` bigint(20) NOT NULL,
`MODIFIED_BY` bigint(20) NOT NULL,
`MODIFIED_ON` bigint(20) NOT NULL,
`NODE_ID` bigint(20) NOT NULL,
`ACCESS_TYPE` varchar(256) CHARACTER SET latin1 COLLATE latin1_bin NOT NULL,
`ENTITY_TYPE` varchar(256) CHARACTER SET latin1 COLLATE latin1_bin NOT NULL,
`SERIALIZED_ENTITY` mediumblob
)
CREATE TABLE `NODE_ACCESS_REQUIREMENT` (
`NODE_ID` bigint(20) NOT NULL,
`REQUIREMENT_ID` bigint(20) NOT NULL,
PRIMARY KEY (`NODE_ID`, `REQUIREMENT_ID`)
)
CREATE TABLE `EVALAUTION_ACCESS_REQUIREMENT` (
`EVALUATION_ID` bigint(20) NOT NULL,
`REQUIREMENT_ID` bigint(20) NOT NULL,
PRIMARY KEY (`NODE_ID`, `REQUIREMENT_ID`)
) |
| Code Block |
|---|
CREATE TABLE `ACCESS_APPROVAL` (
`ID` bigint(20) NOT NULL AUTO_INCREMENT,
`ETAG` bigint(20) NOT NULL,
`CREATED_BY` bigint(20) NOT NULL,
`CREATED_ON` bigint(20) NOT NULL,
`MODIFIED_BY` bigint(20) NOT NULL,
`MODIFIED_ON` bigint(20) NOT NULL,
`REQUIREMENT_ID` bigint(20) NOT NULL,
`ACCESSOR_ID` bigint(20) NOT NULL,
`ENTITY_TYPE` varchar(256) CHARACTER SET latin1 COLLATE latin1_bin NOT NULL,
`SERIALIZED_ENTITY` mediumblob
)
|
Data Access Object (DAO)
We have DAOs for AccessRequirement and AccessApproval objects. In addition to basic CRUD operations we have:
- AccessRequirementDAO.getForNode(), which returns all the AccessRequirements associated with a Node/Entity
- AccessApprovalDAO.getForNode(), which returns all the AccessApprovals associatd with a Node/Entity. This allows us to find all the users who have been given access to an entity via a single database query.
- AccessApprovalDAO.getForAccessRequirementsAndPrincipals() which returns the AccessApprovals for a given list of AccessRequirements and Principals. This method allows us to look up the approval of all the access requirements for a given node (focussing on user of interest) with a single database query.
JSON Schema
We introduce JSON schemas for the generic interfaces AccessApproval and AccessRequirement, and schemas for specific types, TermsOfUseAccessRequirement, TermsOfUseAccessApproval (for tier 2 data), ACTAccessRequirement, and ACTAccessApproval (for tier 3 data).
Services
| Action | URI | Method | Request Body | Authorization |
| create AccessRequirement | /accessRequirement | POST | extension of AccessRequirement.json | ACT membership |
| create 'lock' Access Requirement | /entity/{id}/lockAccessRequirement | POST | N/A | CREATE or UPDATE access to the entity |
| read paginated list of all AccessRequirement objects for an entity. This includes both requirements applied directly to the entity and those applied to its ancestors. | /entity/{entityId}/accessRequirement | GET | VariableContentPaginatedResults<AccessRequirement> | ALL |
| read paginated list of all AccessRequirement objects for an evaluation | /evaluation/{evaluationId}/accessRequirement | GET | VariableContentPaginatedResults<AccessRequirement> | ALL |
| read paginated list of all AccessRequirement objects for a team | /team/{teamId}/accessRequirement | GET | VariableContentPaginatedResults<AccessRequirement> | ALL |
| Retrieve paginated list of unfufilled access requirements (of type DOWNLOAD) for an entity. This includes both requirements applied directly to the entity and those applied to its ancestors. | /entity/{entityId}/accessRequirementUnfulfilled | GET | VariableContentPaginatedResults<AccessRequirement> | ALL |
| Retrieve paginated list of unfufilled access requirements (of type DOWNLOAD or PARTICIPATE) for an evaluation. | /evaluation/{evaluationId}/accessRequirementUnfulfilled | GET | VariableContentPaginatedResults<AccessRequirement> | ALL |
| Retrieve paginated list of unfufilled access requirements (of type DOWNLOAD or PARTICIPATE) for a Team. | /team/{teamId}/accessRequirementUnfulfilled | GET | VariableContentPaginatedResults<AccessRequirement> | ALL |
| update AccessRequirement | /accessRequirement/{accessRqmtId} | PUT | extension of AccessRequirement.json | ACT membership |
| delete AccessRequirement (along with all approvals granted for the requirement) | /accessRequirement/{accessRqmtId} | DELETE | ---- | ACT membership |
| create AccessApproval | /accessApproval | POST | extension of SelfSignAccessApproval.json | ALL |
| ACTAccessApproval.json | ACT membership | |||
| Read all AccessApproval objects for a given entity. This includes the approvals both for the access requirements applied directly to the entity and those applies to the entity's ancestors. | /entity/{entityId}/accessApproval | GET | VariableContentPaginatedResults<AccessApproval> | ACT membership |
| read all AccessApproval objects for a given evaluation | /evaluation/{evaluationId}/accessApproval | GET | VariableContentPaginatedResults<AccessApproval> | ACT membership |
| read all AccessApproval objects for a given team | /team/{teamId}/accessApproval | GET | VariableContentPaginatedResults<AccessApproval> | ACT membership |
| delete AccessApproval | /accessApproval/{accessApprovalid} | DELETE | -- | ACT membership
|
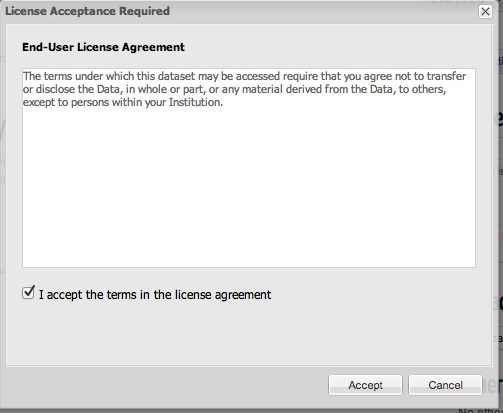
Web UI
When a user clicks Download on the page for a Data object having a Terms of Use access requirement, they are presented with a dialog showing the text from the access requirement, as shown below. If they accept the terms, then an access approval is created and the Download link is presented.
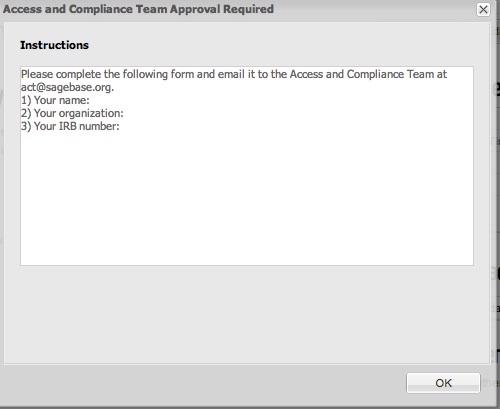
When a user clicks Download on the page for a Data object having an ACT access requirement, they are presented with a dialog showing the text from the access requirement, as shown below. Once they contact the ACT team, someone from the team may create the approval object on their behalf, after which they may download the Data without encountering the dialog.